Bahasa Pemrograman Terpopuler – Sebelumnya kita telah mempelajari perihal pemrograman dasar yang meliputi penjelasan singkat perihal definisi dan kegunaan bahasa pemrograman. Contoh Bahasa Pemrograman itu seperti apa sih ? Berikut pembahasannya.
Sebuah website survei programmer tiap-tiap tahunnya mengadakan survei dengan responden yang berasal dari semua dunia. Surveinya yakni seputar :
– Bahasa pemrograman apa yang paling banyak
digunakan
– Pendidikan para developer/ programmer
– Metode belajar waktu mempelajari coding
seperti apa
– dan survey lainnya.
Menurut survey, kurang lebih ada 16 type bahasa pemrograman yang paling banyak digunakan terhadap th. 2018 berasal dari sekian banyak bahasa pemrograman. Apa saja jenis-jenis bahasa pemrograman tersebut ? inilah ulasan singkatnya. taruhan bola
1. Bahasa Pemrograman JavaScript
Contoh bahasa pemrograman yang pertama yakni JavaScript. sbobet365
Dilansir berasal dari wikipedia JavaScript merupakan salah satu bahasa pemrograman tenar di internet. JavaScript sanggup bekerja disebagian besar browser tenar yakni : Internet Explorer, Google Chrome, Mozilla Firefox, Opera dan lainnya. Kode-kode JavaScript sanggup disisipkan di di dalam halaman web site memanfaatkan tag script. www.americannamedaycalendar.com
Umur bahasa pemrograman ini memang telah 20
tahunan. Dan di dalam kurun waktu tersebut kini JavaScript jadi bahasa
pemrograman yang paling tenar di dunia. Hampir semua web site ataupun blog yang
moderen saat ini ini telah memanfaatkan JavaScript. Karena dengan memanfaatkan
Javascript web site sanggup jadi interaktif dan dinamis.
2.
Bahasa Pemrograman Java
Bahasa pemrograman Java yakni salah satu
semisal bahasa pemrograman yang sanggup dijalankan diberbagai komputer
(PC/laptop) terhitung Handphone/ Smartphone. Sebelum Javascript menduduki peringkat
pertama sebagai bahasa pemrograman paling tenar Java telah lebih dulu berada
terhadap posisi tersebut.
Mengapa demikianlah ? dikarenakan
kebanyakan aplikasi android yang kita memanfaatkan tiap-tiap hari dikembangkan
memanfaatkan bahasa pemrograman Java. Java sendiri mengadopsi banyak kode-kode
(sintak) berasal dari bahasa C dan C++.
Slogan java yang tenar yakni ” Tulis
sekali, melakukan dimanapun”. Slogan itu sesuai dengan kegunaan berasal dari
java yang amat mungkin aplikasi sanggup berlangsung di sebagian Sistem Operasi
(Operating System ) yang berbeda.
3. Bahasa Pemrograman Python
Dikutip berasal dari petanikode.com Phyton
merupakan salah satu bahasa pemrograman yang paling ringan dipelajari waktu ini
dibandingkan dengan bahasa pemrograman lainnya.
Python sendiri ternyata telah banyak
digunakan oleh para developer untuk membuat bermacam macam program aplikasi,
diantaranya : Website, Internet of Things (IoT), Aplikasi Hacking, Aplikasi
Command Line Interpreter, Apbile Mobile, Aplikasi Desktop, dan lain sebagainya.
Struktur sintak Python amat rapi dan cepat
dipahami. Makanya bahasa pemrograman ini amat sesuai dipelajari untuk pemula
yang baru mendambakan belajar menulis kode-kode program (coding).
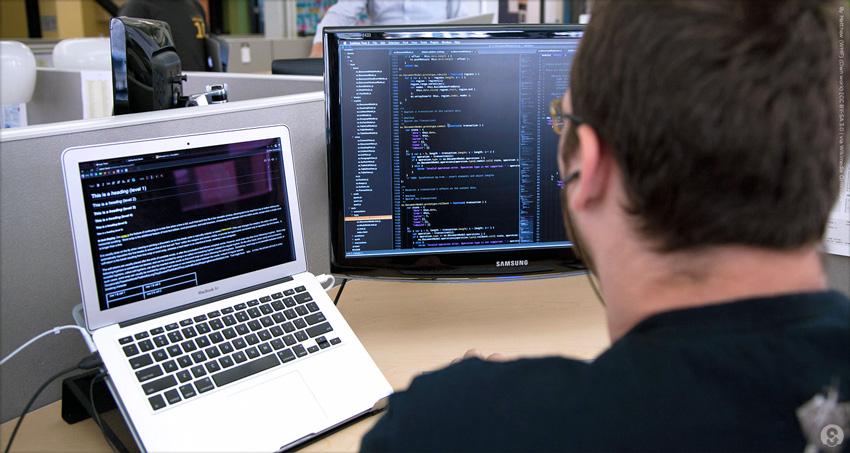
4. Bahasa Pemrograman C#
Menurut wikipedia C# yakni bahasa
pemrograman berorientasi objek yang dikembangkan oleh perusahaan Microsoft
sebagai bagian berasal dari inisiatif kerangka NET Framework. C# dibaca sebagai
C Sharp. Tanda pagar (#) yang dipakai bukanlah merupakan isyarat kres.
Bahasa C# telah terpengaruh oleh banyak
aspek atau fitur yang terdapat terhadap bahasa pemrograman lain seperti :
Delphi, Visual Basic, Java dan banyak ulang lainnya sudah pasti dengan bermacam
penyederhanaan.
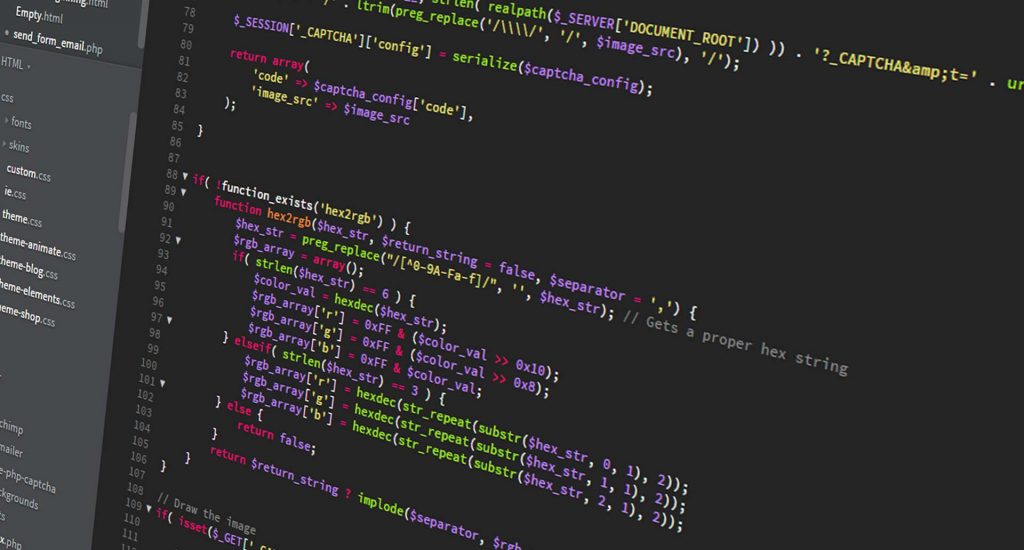
5. Bahasa Pemrograman PHP
Contoh bahasa pemrograman berikutnya yaitu
PHP.
PHP atau Hypertext Preprocessor merupakan
bahasa pemrograman yang digunakan dari sisi server. Bahasa pemrograman ini
disisipkan ke dalam HTML. PHP sendiri banyak dipakai untuk membuat /
mengembangkan situs web yang dinamis.
CMS (content management system) pun sanggup
dibuat gunakan bahasa pemrograman Php. WordPress, blogger, open cart dan yang
lainnya terkandung kode-kode program PHP di dalamnya. Di Indonesia sendiri
komunitas/ group PHP Indonesia di facebook adalah group yang paling aktif menurut
aku dibandingkan group pemrograman yang lainnya.
6. Bahasa Pemrograman C++
Bahasa pemrograman C++ merasa dikembangkan
pada tahun 1970. Bahasa ini merupakan turunan dari Bahasa pemrograman C. Dimana
bahasa pemrograman C++ juga juga ke salah satu bahasa yang berorientasi objek
umumnya disebut dengan Object Oriented Programming.
Mulanya bahasa C++ ini dikembangkan untuk
bahasa pemrograman yang dapat dikerjakan pada proses operasi Unix. Namun bahasa
pemrograman C++ kini menjadi versi dominan.
7. Bahasa Pemrograman C
Dikutip dari wikipedia Bahasa pemrograman C
merasa dikembangkan pada tahun 1972 untuk Sistem Operasi Unix di Bell Telephone
Laboratories. Bahasa pemrograman C ini terlampau besar pengaruhnya bagi bahasa
kondang lainnya layaknya : C++, Java, Objective – C, dan lainnya.
Bahasa pemrograman ini dibuat untuk
memprogram proses dan jaringan komputer. Namun sering juga digunakan untuk
mengembangkan software aplikasi beraneka style platform OS, arsitektur
komputer, bahkan beberapa compiler yang kondang udah tersedia.
8. Bahasa Pemrograman TypeScript
Menurut codepolitan.com TypeScript adalah
bahasa pemrograman yang basisnya adalah JavaScript. Dengan menambahkan fitur
strong-typing dan rancangan pemrograman objektif atau OOP klasik.
Dilihat dari dokumentasinya, bahasa ini
disebut sebagai superset dari JavaScript. Kesimpulannya kode-kode JavaScript
adalah kode-kode TypeScript juga.
Untuk mengembangkan aplikasi kompleks akan
lebih enteng terkecuali pakai TypeScript dikarenakan bahasa ini tawarkan class,
modul, dan interface.
9. Bahasa Pemrograman Ruby
Ruby merupakan bahasa pemrograman yang
dinamis, refletif, elegan, dan berbasis objek. Menurut situs ruby-lang.org ”
Ruby adalah sobat terbaik programmer “. Ruby bersifat open source, enteng
dimengerti, dan produktif. Kode-kode Ruby cukup elegan, naturan, enteng dibaca
dan ditulis.
Ruby punyai manfaat yang terlampau bagus.
Diantaranya mampu digunakan untuk membawa dampak aplikasi web, GUI, dan banyak
lagi. Salah satu platform yang dikembangkan pakai bahasa Ruby adalah Twitter.
10. Bahasa Pemrograman Swift
Swift yakni bahasa pemrograman untuk
pengembangan iOS dan OS X yang dikembangkan oleh perusahaan Apple. Swift
didesain untu berdampingan dengan Objective-C dan hindari program dari kode
yang salah.
Pertama kali dikenalkan oleh Apple pada
acara tahunan WWDC 2014. Dibangun dengan compiler LLVM yang termasuk dalam
XCode.
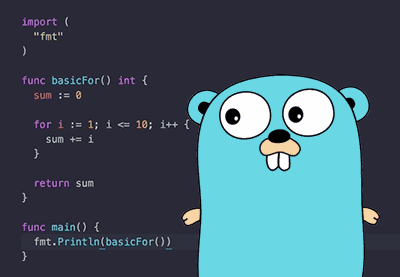
11. Bahasa
Pemrograman Go
Bahasa
pemrograman Go sering disebut terhitung Golang yakni bahasa pemrograman yang
dibikin oleh perusahaan Google pada th. 2009.
Semacam bahasa
pemrograman lainnya Go lang pun merupakan pengembangan dari bahasa pemrograman
C dengan gabungan dari sebagian bahasa lain layaknya : Pascal, Modula, Oberen,
atau lain sebagainya.
Aplikasi-aplikasi
yang dikembangkan memakai bahasa pemrograman Go antara lain : Dropbox,
Soundcloud, Cloudfare, Docker, dan Google.
12. Bahasa
Pemrograman Kotlin
Kotlin merupakan
bahasa pemrograman dengan pengetikan statis dan terjadi pada Mesin Virtual Java
atau JVM. Kotlin bisa terhitung dikompilasikan ke dalam wujud source code
JavaScript.
Kotlin sengaja dibikin untuk bisa bekerjasama dengan bahasa Java lebih-lebih bergantung pada library yang ada pada pemroraman Java. Google sudah mengumuman bahasa pemrograman Kotlin kini sudah menjadi bahasa formal untuk mengembangkan aplikasi-aplikasi android tak sekedar Java dan C .
13. Bahasa
Pemrograman Perl
Dilansir dari
Wikipedia Perl adalah bahasa pemrograman yang dikembangkan oleh Larry Wall di
mesin Unix. Rilis pertama pada tanggal 18 Desember 1987. Tersedia pula untuk
beraneka Sistem Operasi.
Meskipun banyak
bahasa pemrograman yang baru saat ini tapi Perl masih selalu kokoh. Artinya
masih banyak pengguna Perl saat ini. Salah satunya gara-gara bahasa perl
bersifat dinamis dan bisa digunakan untuk mengembangkan banyak program
aplikasi.
14. SQL
SQL (Structured
Query Language ) merupakan bahasa yang digunakan untuk mengakses data dalam
database relasional. Bahasa ini merupakan bahasa standar yang digunakan di
dalam manajemen basis data. Saat ini hampir seluruh server basis information
membantu bahasa SQL untuk jalankan manajemen datanya.
15. Bahasa
Pemrograman VBA (Visual Basic for Application)
Contoh bahasa
pemrograman yang ke 15 yaitu VBA.
VBA (Visual Basic
for Application) merupakan sebuah bahasa turunan dari bahasa Visual Basic yang
terhitung dikembangkan oleh Microsoft.
VBA sendiri
merupakan paduan yang terintegrasi pada lingkungan pemrograman Visual Basic
Editur bersama dengan bahasa pemrograman Visual Basic di dalam aplikasi utama
Microsoft Office yang dimaksudkan untuk aplikasi-aplikasi tertentu.
Fungsi utama dari
VBA yaitu mengakibatkan otomatisasi pekerjaan yang dilaksanakan secara
berulang-ulang dan kompleks. VBA cuma bisa dibangun terhadap aplikasi utama
Microsoft Office. Misalkan di microsoft excel kami bisa mengakibatkan aplikasi
pendataan bersama dengan bantuan VBA ini.
16. HTML dan CSS
HTML yaitu bahasa
markup yang dipakai untuk membuat sebuah website. HTML berfungsi untuk
menampilkan informasi di Internet. Sedangkan CSS merupakan kode-kode yang
mengatur tampilan dari HTML.
Itulah 16 contoh bahasa pemrograman yang saat ini cukup populer digunakan oleh para developer. Masih banyak jenis-jenis bahasa pemrograman yang tidak dibahas disini.
Continue Reading